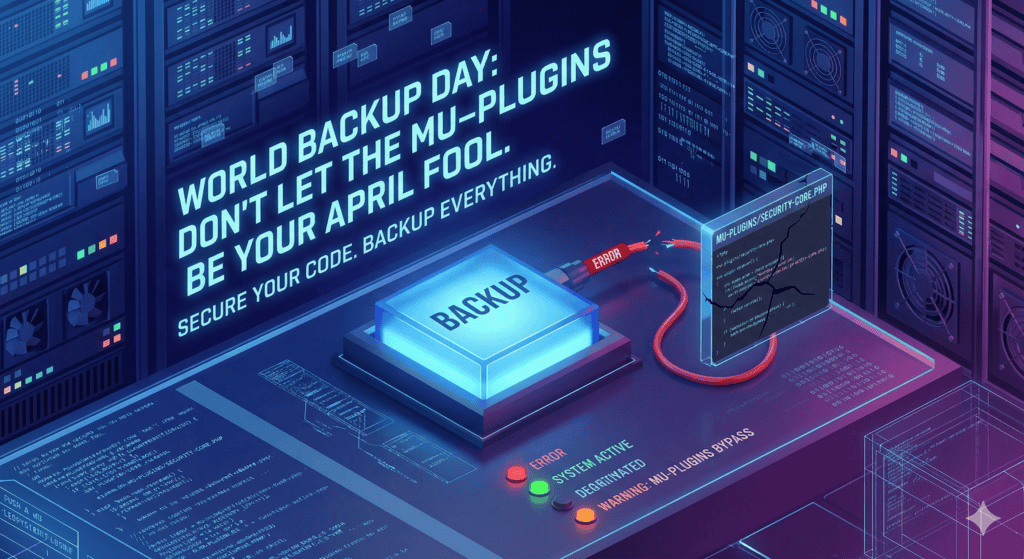
Today is World Backup Day, and if you are managing sites for clients, volunteers, or yourself, you have probably heard the 3-2-1 rule—or my personal, paranoid favorite, the 4-3-2-1 method. You back it up every month, you glance at the staging restore, it looks fine, and you move on.
Never just glance. Look closer. You might have secured the login and restricted user privileges to the Editor role, but have you checked the Drop-ins or the Must-Use (mu-plugins) folder lately? If you see scripts there that you did not install, or PHP files hiding in your uploads folder, it is time for a reality check. Your successful restore might just be restoring a backdoored headache that is waiting for the right moment to wake up.
The Invisible Intrusion
In the last 48 hours, I fought a ghost in the machine for a client. The site looked perfect when logged in, but for public users on specific ISPs, it was a mess. It was not just a bad plugin; it was a combination of malicious mu-plugins that did not belong there and DNS poisoning or caching at the ISP level that made the site look infected on PCs while 5G mobiles and VPNs showed a clean site. To make matters worse, the router ARP tables were holding onto dirty records like a stubborn gremlin.
To rule out local software issues, I tested the site across multiple Virtual PCs, various operating systems, and every major browser. In those isolated environments, the site looked perfectly fine, which confirmed that the issue was not a universal site failure but a targeted local network or ISP hallucination.
The Fix
I did not just restore; I sanitized. This involved nuking the rogue mu-plugins and scrubbing the uploads directory of any PHP strays that had no business being in a media folder. I switched the local environment to AdGuard DNS to bypass those frustrating ISP hallucinations and rebuilt the site from the ground up to ensure the backup of the backup is 100 percent clean.
Conclusion
If you are not sure what a file does, ask an LLM or an AI, as they are excellent at spotting malware patterns in code. Do not be the April Fool tomorrow because you were too lazy to check your wp-content today.